TL;DR – We quantified the pervasiveness of online brand impersonation attacks against regional banks, community banks, and credit unions during the first quarter of 2022 – download the report now.
Have you ever received a text message like the one in this image?
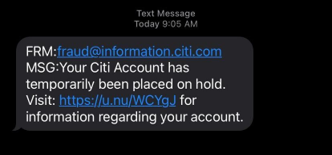
Of course you have. A mobile device user that hasn’t found themselves targeted by a mass smishing campaign impersonating a globally recognized bank would be a rare specimen indeed!
A lesser known target of online brand impersonation
It’s obvious to all of us that cybercriminals impersonate the top financial brands online to dupe employees and consumers and steal credentials, identities, money, and more. Some regional banks and credit unions, however, are surprised to learn that spoof websites masquerading as smaller institutions like them is a growing threat.
A number of regional banks, community banks, and credit unions assume they’re not widely known enough to attract fraudsters’ attention online. Our automated analysis of at least 50 million websites a day (a number that continues to grow) disproves this theory. We found that in just the first 90 days of 2022, 20 percent of regional bank and credit union brands in our data sample experienced online brand impersonation attacks
Solving the online brand impersonation problem starts with quantifying it
Allure Security makes it our mission to rid the Internet of scams. In pursuit of that mission we educate businesses about scams targeting their organization and their patrons. For this reason, we poured many hours of data analysis and research into a study that measures the pervasiveness of spoof websites targeting smaller financial institutions.
Many times these institutions set themselves apart from larger institutions with more personal service and/or more intimate customer experiences. Erosion of patrons’ perception of their brands’ trustworthiness is quite literally a dealbreaker.
The following are only a few of the myriad ways online brand impersonation attacks damage credit union and regional bank brands, as well as, harm their bottom lines:
- Customers churn or don’t convert because they don’t trust the brand
- Reduced customer satisfaction
- Increased customer service wait times as the result of an incident
- Costly investigations
- Costs of reimbursing victims for losses
By quantifying the problem, we think people will take it more seriously and plan accordingly. Especially important is our evaluation of the effectiveness of monitoring for permutations of a brand’s domain name (e.g., acmebank.com vs. acrnebank.com).
Long story short, those approaches, sometimes referred to as domain monitoring, are no longer effective (if they ever were). Simply looking for “lookalike” domains only caught about a third of attacks. That leaves a ton of online brand risk unmitigated and customers exposed.
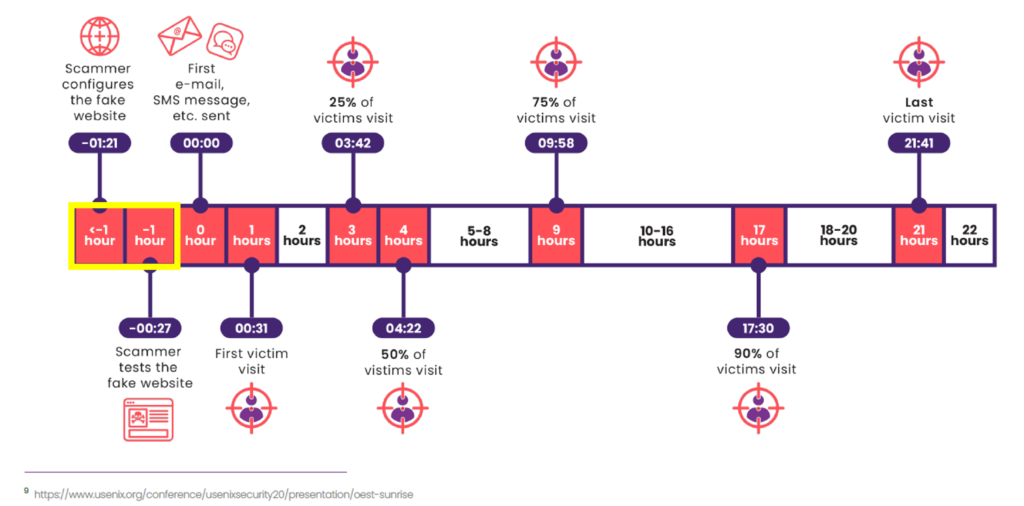
Can a scam website be stopped before it tricks a single person?
The best way to just about eliminate the risk of customers falling victim to a scam website is to detect those sites in the early stages, when a fraudster is setting it up, but before they’ve distributed the scam via email, SMS, QR code, messaging app, etc. This is indeed possible. We do it continually for our customers by way of our AI-powered online brand impersonation-as-a-service. This can’t be achieved by searching for and evaluating lookalike domains which would require hundreds of person hours anyway.
We’ve had the opportunity to share a preview of the report with a number of leaders at community banks, regional banks, and credit unions. They’ve found the data informative and actionable, and we plan to provide the community with further updates and trend analysis over time.
Download the full report to get more details and potentially sift out a stat or two you can use to start an internal conversation today about modernizing your online brand protection program.